How It Works
Myrad uses a privacy-first verification system built for both users and enterprises.
Verification happens on the user's device.
Only cryptographic proof results are shared.
Raw data never leaves the user.
User Participation Model
Myrad is designed so individuals benefit without exposure.
What Users Do
| Action | Description |
|---|---|
| Contribute verified activity | Connect apps and verify digital activity |
| Never submit raw data | Data stays on device, only proofs are shared |
| Earn points and rewards | Every verified contribution is compensated |
| Opt out at any time | Participation is voluntary and reversible |
Participation is voluntary, transparent, and reversible.
For Users
Your Privacy Guarantees
- We never store your raw data
- Your data becomes anonymous signals
- You earn without being tracked
- You can leave anytime
Step 1: Quick Onboarding
Sign up using email or social login.
No wallets, no technical setup.
Step 2: Connect Your Apps
Connect apps like Zomato, GitHub, or Netflix.
Verification is powered by Reclaim Protocol and runs locally on your device.
Your raw data is never accessed or stored.
Step 3: Privacy-First Verification
A cryptographic proof confirms your activity is real without revealing:
- Personal details
- Activity history
- Account data
Only anonymous proof results are generated.
Step 4: Earn Rewards
Each successful verification earns you points.
No profiles. No tracking. No surveillance.
Rewards update in real time and can be redeemed anytime.
How to Contribute
Watch the Tutorial
Contribution Steps
- Install the Reclaim verified app (Play Store / App Store)
- Connect supported accounts anonymously
- Complete verification securely
- Submit verified proofs
- Earn points for each valid contribution
- Climb the leaderboard
For Enterprises
Myrad provides verified human behavior signals without exposing user data.
Enterprise Guarantees
- No PII: Personal identifiers never included
- No user profiles: No individual-level access
- Aggregated only: Cohort-based outputs
- Auditable pipeline: Full transparency
What Enterprises Get
| Capability | Description |
|---|---|
| API Access | Aggregated, privacy-safe signals via APIs |
| Proof-Backed Data | Every signal is cryptographically verified |
| Consent-First | All data is opt-in by design |
| Compliance-Ready | Built for GDPR, CCPA, and future regulations |
Delivered Value
- Verified human behavior in aggregated form only
- No tracking or individual-level access
- Ethical, consent-driven data sourcing
- Full transparency through an auditable pipeline
The Privacy-First Flow
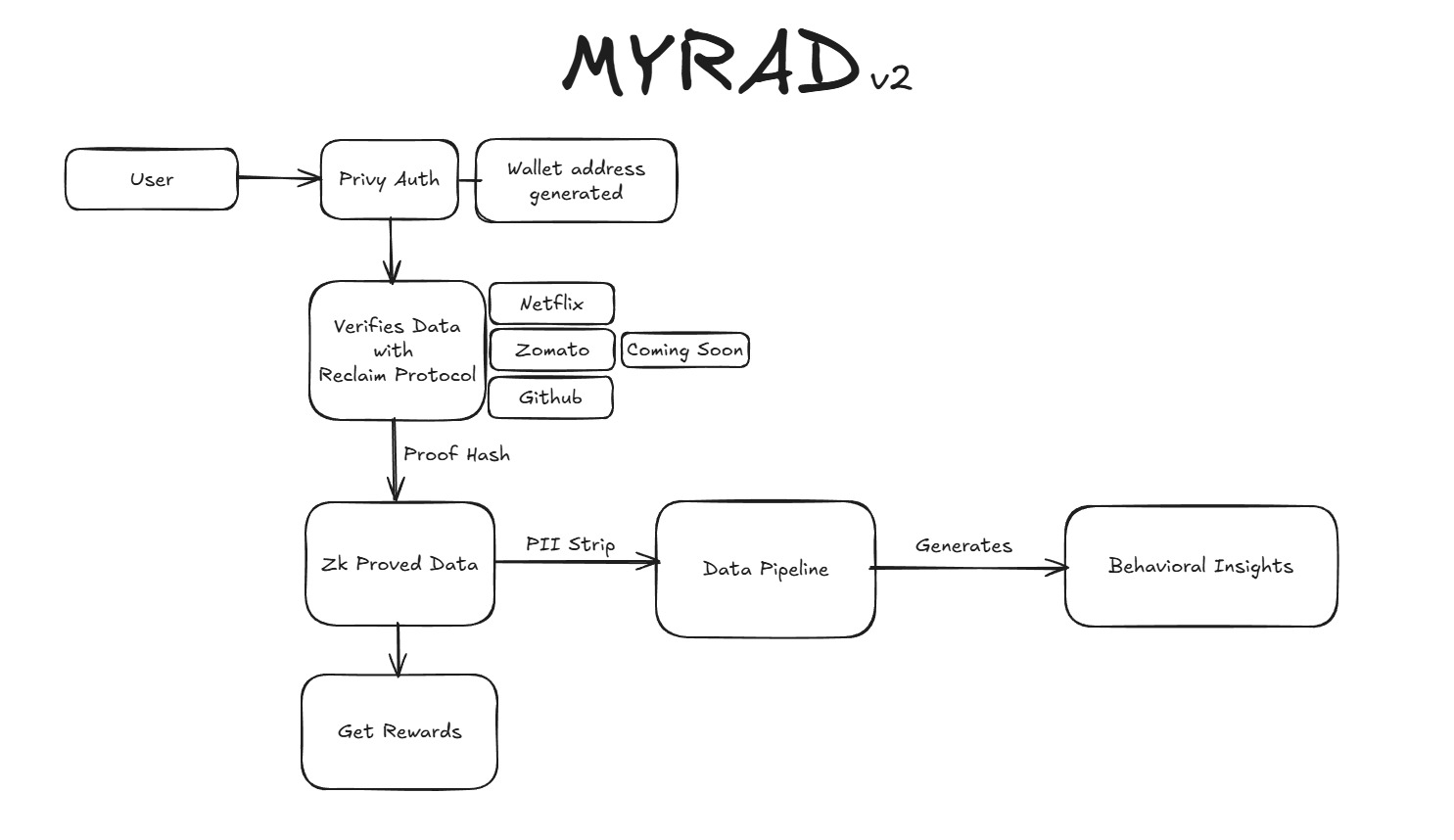
Verification happens on the user's device.
Only proof results are shared.
Raw data never leaves the user.